Graphene Technologies Houston IT security helps businesses protect sensitive data while employees work from anywhere. Today, remote work extends beyond the office into homes, coffee shops, and shared spaces. However, these environments introduce serious risks. Therefore, companies must act quickly to strengthen their cybersecurity strategies.
As remote work continues to grow, businesses need clear policies and strong tools. Otherwise, employees may unknowingly expose company data. Fortunately, Graphene Technologies delivers reliable solutions that keep your workforce secure in every location.
The Risks of Public Wi-Fi Networks
Public Wi-Fi attracts remote workers because it is convenient and free. However, it also creates major security vulnerabilities. In many cases, these networks lack encryption. As a result, attackers can intercept data within seconds.
Moreover, cybercriminals often create fake networks that appear legitimate. For example, a network labeled “Free Coffee Shop Wi-Fi” may actually belong to a hacker. Once an employee connects, the attacker can monitor activity and steal credentials.
Therefore, businesses must train employees to avoid unsecured networks. Even password-protected Wi-Fi can pose risks if widely shared. Instead, companies should enforce strict usage policies to reduce exposure.
Why VPNs Are Essential for Remote Security
A Virtual Private Network (VPN) protects data by encrypting internet traffic. Because of this, hackers cannot read sensitive information. For this reason, VPN usage should be mandatory for all remote employees.
In addition, companies should configure VPNs to connect automatically. This step removes user error and ensures consistent protection. At Graphene Technologies, we help Houston businesses deploy secure, easy-to-use VPN solutions.
Furthermore, technical controls can block access to company systems without a VPN. This approach guarantees compliance and strengthens your overall security posture.
Prevent Visual Hacking in Public Spaces
While digital threats increase, physical risks also remain. For instance, someone nearby can easily view a laptop screen. This tactic, known as visual hacking, requires no technical skill.
Therefore, employees must stay aware of their surroundings. Sensitive data, such as financial reports or client records, should never be visible in public. To reduce this risk, businesses should provide privacy screen filters.
Additionally, employees should position screens away from others whenever possible. These simple steps significantly improve data protection.
Strengthen Physical Device Security
Employees often underestimate the risk of device theft. However, leaving a laptop unattended in a public place invites trouble. Thieves act quickly, especially in busy environments.
To prevent this, employees must keep devices within reach at all times. Moreover, using cable locks adds an extra layer of protection. Although not foolproof, these tools discourage opportunistic theft.
At the same time, awareness plays a key role. When employees stay alert, they can identify and avoid risky situations.
Protect Conversations and Sensitive Information
Even in noisy environments, conversations can be overheard. Therefore, discussing confidential information in public creates unnecessary risk.
Instead, employees should move to private areas when handling sensitive calls. For example, stepping outside or sitting in a car offers more privacy. While headphones help, they do not prevent others from hearing one side of the conversation.
Consequently, clear communication guidelines must be part of your remote work policy.
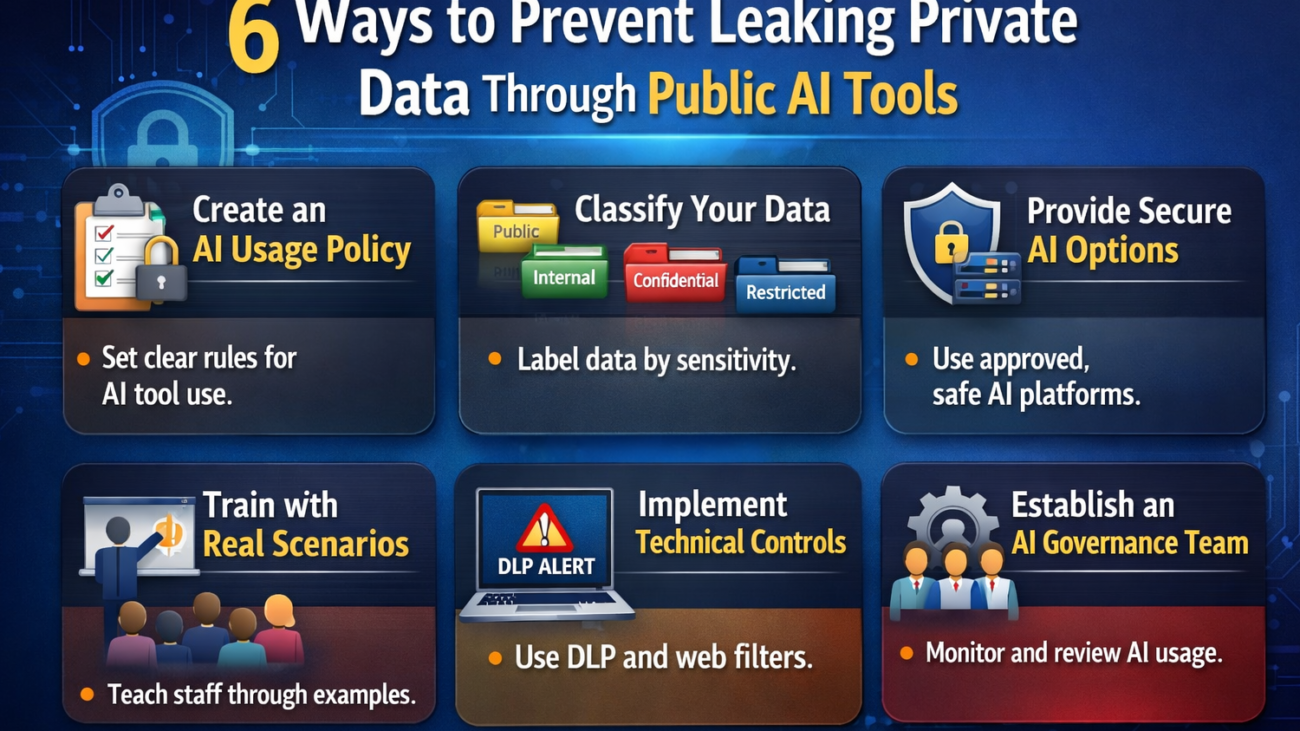
Build a Clear Remote Work Security Policy
A strong policy removes confusion and sets expectations. Employees need clear instructions on how to handle public Wi-Fi, devices, and conversations.
In addition, businesses should explain why each rule matters. When employees understand the risks, they are more likely to comply. Graphene Technologies helps Houston companies create effective, easy-to-follow security policies.
Moreover, companies should review policies regularly. As threats evolve, your strategy must adapt. Updating guidelines ensures long-term protection.
Empower Your Workforce with Graphene Technologies Houston IT Security
Remote work offers flexibility, but it also demands responsibility. Therefore, businesses must invest in the right tools and training.
Graphene Technologies Houston IT security provides comprehensive solutions that protect your business from modern threats. From secure remote access to employee training, we help you stay ahead of cyber risks.
If your team works remotely, now is the time to act. Strengthen your defenses and protect your data—no matter where your employees log in.